When data protection becomes a business priority, our sovereign cloud stack becomes the answer.


The growing need for full data control is met with limited options, as the global duopoly ecosystem continues to centralize access and restrict autonomy. We solve this by delivering a sovereign cloud stack that gives you full ownership, complete visibility, flexible governance, and control over how, where, and by whom your data is managed. It’s a secure, future-ready solution designed to put your organization back in command.
As a cloud infrastructure provider that coexists alongside major
players, DesktopIP is committed to building true digital
sovereignty—by keeping your data secure, compliant, and
respectful of regulatory boundaries.
We don’t exploit
or overlook your data. Instead, we treat it with the seriousness
and integrity it deserves—as something that truly belongs to
you.

See how we work. Step by step. Decision by decision. We help you claim your ground and stand tall with your digital independence goal.
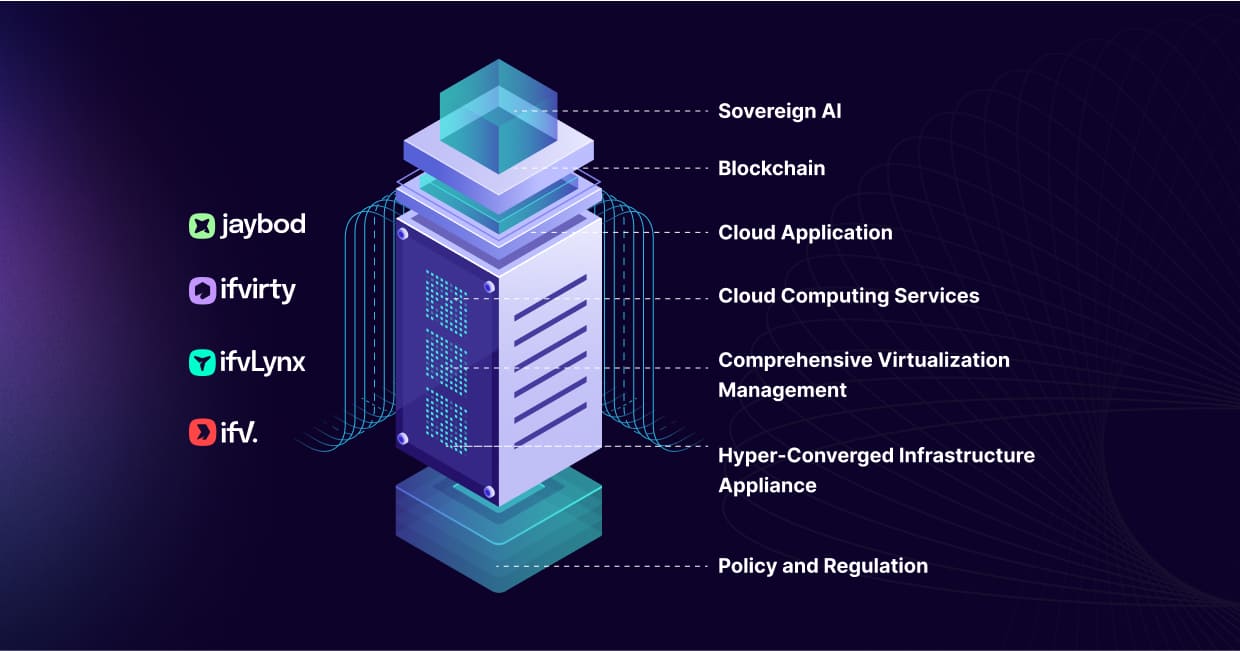
We deliver a complete digital ecosystem—from sovereign, secure cloud infrastructure (Ifvirty, IFVLynx, IFV) to tailored SaaS applications (Jaybod)—designed for seamless, interconnected operations. Our proprietary "Magic Sauce," keeps your data within national borders, ensures compliance with local laws, and protect against external threats with strict, transparent protocols and an end-to-end protection model. With your own Sovereignty Tower, you call the shots—where your data lives, how it flows, and who touches it. Full-stack control, zero compromise.
Your data is valuable. No more overlooked on your data’s privacy.